TL;DR: Most organizations manage each regulatory framework in isolation – separate teams, separate trackers, separate evidence packs. When frameworks overlap (and in Vietnam's regulatory landscape, they always do), this siloed approach creates duplicated work, contradictory controls, and evidence gaps that only surface during inspections.
Multi-framework compliance is not about doing more work – it is about doing the same work once and mapping it to every framework that requires it. This article explains how overlapping obligations actually work, why framework silos fail under regulatory pressure, and how operational compliance architecture eliminates duplication while strengthening evidence across every framework simultaneously.
This article is written for DPOs, compliance managers, audit leads, legal counsel, and governance teams – especially those operating under multiple Vietnamese regulatory frameworks where obligations overlap, deadlines intersect, and a single data processing activity can trigger requirements under three or four laws simultaneously.
The inspection that exposes the silos
An internal audit lead receives notice of a regulatory inspection covering personal data processing, cybersecurity controls, and cross-border data transfers. That means multiple frameworks are in scope at the same time, and the evidence required by each one overlaps more than most organizations expect.
The audit lead asks three different teams for their evidence packs. Each team produces documents independently. The PDPL team has their DPIA dossiers. The cybersecurity team has their incident response records and data localization evidence. The data governance team has their classification inventories and sharing logs.
When the audit lead tries to assemble a consolidated response, the problems become visible immediately: the data inventory referenced in the PDPL filing does not match the classification scheme used by the data governance team. The vendor list in the cybersecurity evidence does not include two processors that appear in the cross-border transfer assessment. The approval history for a key control exists in one team's tracker but is missing from another's.
“Framework silos duplicate work and produce contradictory evidence. And contradictory evidence is worse than no evidence at all.”
The inspection has a deadline. The remediation required is not technical – it is architectural. The organization was doing compliance work across every framework. But the work was never connected. Each team operated as if their framework existed in isolation, when in reality the same data, the same vendors, the same processing activities, and the same controls are governed by multiple laws simultaneously.
Why frameworks overlap – and why organizations pretend they do not
Vietnam's regulatory landscape in 2026 includes at least six active frameworks that touch data governance, privacy, and security: the PDPL (Law on Personal Data Protection 2025), its implementing Decree 356 on cross-border transfers, the Vietnam Data Law, the Cybersecurity Law 2025, the AI Law 2026, the E-Commerce Law 2025, and the Telecommunications Law 2023.
Vietnam's active frameworks share significant common ground:
- Cross-border data transfers appear in both the PDPL (Decree 356) and the Data Law's governance requirements.
- Authority request handling spans the PDPL, Cybersecurity Law, and Telecommunications Law.
- Data localization requirements overlap between the Cybersecurity Decree 53 and the PDPL.
- Data classification and inventory obligations exist in both the Data Law and the PDPL.
- Vendor and processor governance requirements appear across the PDPL, Data Law, and Cybersecurity frameworks.
Despite these overlaps, most organizations manage each framework separately. The reason is simple: frameworks arrive separately. A new law is passed. A team is assigned. A compliance project is launched. By the time the next framework appears, the first team has already built their own tracking system, their own templates, their own evidence repository. Connecting them retrospectively feels like a project nobody has time for.
“Frameworks arrive one at a time. Regulatory inspections do not.”
The result is predictable: each framework team does competent work in isolation, but the organization cannot produce a coherent picture of its compliance posture across frameworks. The DPO or compliance lead who needs to see the full landscape often ends up manually reconciling outputs from multiple teams using different tools, terminology, and classification schemes.
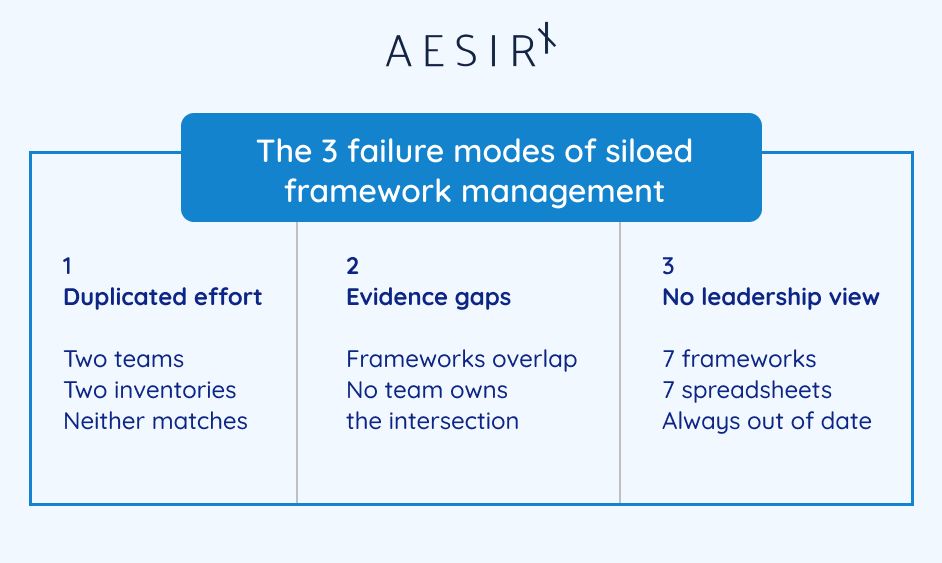
The three failure modes of siloed framework management
Duplicated effort with inconsistent results
When the PDPL team and the Data Law team both need a data inventory, they build separate ones. The PDPL inventory focuses on personal data categories and processing purposes. The Data Law inventory focuses on classification levels and sharing controls. Neither is wrong. But when a regulator asks for "the organization's data inventory," the existence of two different versions – with different scope, different granularity, and different update cycles – creates a credibility problem.
The same pattern repeats across controls: vendor assessments conducted separately for privacy and cybersecurity, access control reviews done independently for PDPL and Telecom requirements, incident response procedures documented in parallel with different escalation paths.
- One data inventory maintained by the privacy team, another by the data governance team.
- Vendor assessments duplicated across frameworks with different risk criteria.
- Access control reviews conducted independently under different review cycles.
- Incident response procedures documented twice with conflicting escalation timelines.
Evidence gaps at the intersection
The most dangerous gaps appear where frameworks overlap but neither team takes ownership. Cross-border transfer governance is a common example: the PDPL team handles the DPIA and filing requirements, while the Data Law team handles the governance attestation. But the actual transfer, the vendor, the recipient jurisdiction, the contractual safeguards, sits between them.
When the regulator asks about a specific transfer, the PDPL team has the filing but not the Data Law governance artifacts. The Data Law team has the attestation but not the cross-border impact assessment. Neither team has a complete picture, and assembling one under inspection pressure takes days.
No cross-framework visibility for leadership
The Enterprise DPO or compliance director who needs to report to the board on ‘regulatory compliance status’ must manually aggregate inputs from each framework team. There is no single dashboard showing maturity across frameworks, no consolidated view of obligation coverage, no way to see which controls satisfy requirements under multiple laws simultaneously.
Board reporting becomes a quarterly exercise in spreadsheet consolidation – and the result is always a snapshot that is already outdated by the time it is presented.
“When you manage frameworks in silos, you can be fully compliant with each one individually and still fail a cross-framework inspection.”
From framework silos to obligation mapping
The shift from siloed framework management to multi-framework operations begins with a simple recognition: regulatory obligations, not frameworks, are the unit of work.
A single obligation – ‘maintain an inventory of personal data processing activities’ – may be required by the PDPL, the Data Law, and the Cybersecurity framework. In a siloed model, three teams maintain three inventories. In an obligation-mapped model, one inventory exists, and it is linked to every framework that requires it.
This is what obligation mapping with RACI governance looks like in practice:
- Each regulatory obligation is identified and catalogued – across all active frameworks.
- Each obligation is mapped to the organizational unit responsible for fulfilling it.
- Responsible, Accountable, Consulted, and Informed roles are assigned per obligation.
- Where obligations overlap across frameworks, the mapping makes the overlap explicit – one control, multiple framework references.
- A cross-framework maturity assessment compares scores across all frameworks in a single consolidated view.
The Enterprise DPO no longer asks "are we compliant with the PDPL?" and "are we compliant with the Data Law?" as separate questions. They ask "which obligations are covered, by whom, and which frameworks does each obligation satisfy?" – and get a single answer.
Framework-to-module mapping – knowing what applies where
Multi-framework compliance requires knowing which parts of the organization – which modules, which teams, which processes – each framework touches. Without this mapping, teams cannot scope their work, and audit leads cannot scope their inspections.
Framework-to-process mapping connects each regulatory framework to the operational areas it actually governs. The PDPL maps to data mapping, consent, rights requests, assessments, and vendor risk. The Data Law maps to data mapping, classification, governance, and vendor management. The Cybersecurity Law maps to incident operations, monitoring, access accountability, and data localization.
This mapping creates clarity:
When a new framework is adopted: the organization immediately sees which modules and teams are affected.
When a framework is updated: the impact assessment routes automatically to the affected module owners.
When an audit is scoped: the framework-to-module mapping determines which evidence sources are relevant.
When a persona – a DPO, a cybersecurity lead, an AI governance officer – needs to understand their scope: the mapping shows exactly which frameworks and which modules fall under their responsibility.
Evidence completeness across frameworks – the inspection-ready dashboard
The single most valuable capability in multi-framework compliance is evidence completeness visibility: a dashboard that shows, by framework, by case, by template, and by evidence type, what is complete and what has gaps.
Consider the Internal Audit Lead preparing for a cross-framework regulatory inspection. Six frameworks are potentially in scope. Without a completeness dashboard, the audit lead must contact each framework owner individually, request status updates, reconcile responses, and manually track down gaps – all under time pressure.
With framework-scoped evidence completeness:
- The audit lead opens an inspection case and selects the frameworks in scope.
- The platform automatically pulls relevant cases, templates, and evidence by framework.
- A completeness dashboard shows status across every framework, every case type, every evidence category.
- Gaps are flagged visibly – not buried in email threads or spreadsheet tabs.
- Tasks are assigned to specific framework owners for missing evidence, with deadlines tied to the inspection timeline.
- The exported audit pack includes framework-by-framework appendices, a gap and exception log, approval history, and linked case summaries.
This is not a reporting feature. It is the operational architecture that makes cross-framework inspections manageable. The audit lead spends their time reviewing evidence quality and closing gaps – not hunting for documents across six different team folders.

Regulatory change management across frameworks
Frameworks do not stand still. Laws are amended. Decrees are issued. Implementation timelines shift. In a multi-framework environment, a single regulatory change can ripple across multiple modules and multiple teams.
Regulatory update tracking with impact assessment provides a structured workflow for managing these changes:
- A framework update is logged with the specific changes, effective date, and source reference.
- The platform routes the update to affected module owners based on the framework-to-module mapping.
- Each affected owner reviews the impact on their controls, processes, and evidence.
- The DPO or compliance director determines the response: no action required, internal remediation needed, or formal filing update (such as an MPS amendment) required.
- If a filing update is required, a linked amendment case is opened using the appropriate official Mẫu số form, for example Mẫu số 03a/03b for Decree 356 dossier updates, or the corresponding filing instrument required under the relevant framework.
- The change, the impact assessment, the decisions, and the remediation actions are all recorded – creating an evidence trail of how the organization responded to regulatory evolution.
In a siloed model, a regulatory change notification arrives and someone must manually determine who is affected. In a mapped model, the routing is automatic because the framework-to-module relationships already exist.
How an audit lead assembles a cross-framework evidence pack
The Internal Audit and Regulatory Inspection Lead at a large enterprise is responsible for regulatory readiness across six frameworks – PDPL, Decree 356, Data Law, E-Commerce Law, Telecommunications Law, Cybersecurity Law, and AI Law. An inspection notice arrives scoped to data governance and cross-border transfers, which implicates at least three frameworks simultaneously.
When an inspection notice arrives, the audit lead opens one inspection case and selects the frameworks in scope, for example PDPL, Decree 356, and the Data Law. The platform then pulls the relevant filings, assessments, evidence artifacts, and governance records into one working pack. A completeness view shows what is fully covered and where gaps remain, such as a pending vendor review or an unsigned governance section. The audit lead assigns those gaps to the right owners, tracks them against the inspection timeline, and routes the finished pack through legal and audit review before export. The result is one coherent cross-framework evidence package rather than multiple disconnected framework folders.
The entire process – from inspection notice to export-ready evidence pack – operates from a single case with cross-framework visibility. The audit lead never needs to chase individual teams for their separate evidence folders. The evidence already exists because it was generated operationally, and the framework mapping tells the platform which evidence belongs to which framework.
How an enterprise DPO consolidates a multi-department filing
The Enterprise DPO at a major financial institution needs to submit a PDPL DPIA dossier that requires input from fifteen departments – retail banking, HR, marketing, IT security, procurement, and more. The same processing activities also trigger Data Law governance requirements and Decree 356 cross-border transfer obligations.
In a siloed model, the DPO would manage three separate processes: one for the DPIA, one for the governance attestation, one for the cross-border assessment. Each process would require the same departments to provide overlapping information through different channels.
In a multi-framework model:
→ The DPO opens a master case and selects the purpose – DPIA filing with linked cross-border and governance components.
→ The platform generates structured section ownership by department, with each department completing their inputs once.
→ As departments submit their sections, the platform auto-consolidates and flags inconsistencies: a vendor listed in the cross-border section that does not appear in the vendor governance section, a classification level in the Data Law attestation that conflicts with the PDPL inventory.
→ The DPO reviews the consolidated output, sends targeted corrections to only the affected departmental sections – not a blanket request to all fifteen departments.
→ Legal and compliance approvals are triggered with the specific version reviewed and the approval conditions recorded.
→ Official Mẫu số forms are generated where applicable, and the filing package keeps a clear distinction between regulator-facing documents, internal working materials, and supporting evidence.
→ The export includes a contributor lineage appendix showing exactly who provided what content, when, and which version was approved.
The fifteen departments did their work once. The evidence satisfies requirements under three frameworks. The contributor lineage proves accountability across the entire chain.
“Multi-framework compliance does not mean doing the work three times. It means doing the work once and making the evidence count everywhere it needs to.”
Use case: The compliance director managing regulatory change across frameworks
A new decree modifies cross-border transfer requirements under the PDPL. The Compliance Director needs to determine: does this affect our current filings? Do we need to amend our MPS submissions? Which teams need to update their controls?
In a mapped model, the regulatory update is logged with the specific changes and effective date. The framework-to-module mapping identifies the affected areas: assessments, vendor risk, data mapping, and program governance. The impact assessment routes to each module owner. The Data Governance Lead confirms that data inventory classifications remain valid. The Cross-Border Transfer Lead identifies two active transfers that require amended filings. The DPO reviews the consolidated impact and decides: internal remediation for the classification confirmation, formal MPS amendment for the two affected transfers.
A linked amendment case is opened with the appropriate official forms. The entire chain – from regulatory change to impact assessment to amendment decision to filing update – is recorded as a single traceable workflow. When the next inspection asks "how did you respond to Decree X amendment?", the answer is not a reconstructed narrative. It is a case with documented decisions, responsible parties, and timestamps.
The shift: from framework compliance to obligation architecture
The organizations that struggle with multi-framework compliance are not under-resourced or under-skilled. They are architecturally siloed. Each framework team is competent. Each team produces valid evidence. But the evidence does not connect, does not cross-reference, and does not present a coherent organizational picture under inspection pressure.
The shift is not about working harder. It is about recognizing that obligations, not frameworks, are the operational unit. A single data inventory satisfies requirements under three laws. A single vendor assessment covers privacy, cybersecurity, and data governance obligations. A single approval chain proves accountability to every framework that requires it.
When your compliance architecture maps obligations to frameworks instead of managing frameworks in isolation, three things change:
Duplicated work disappears – departments provide input once, evidence counts everywhere.
Evidence gaps at framework intersections become visible – because the mapping shows where frameworks share requirements.
Cross-framework inspections become manageable – because the evidence is already connected, not scattered across team silos.
“Compliance maturity is measured by whether your evidence holds together when a regulator pulls on any thread, not by the number of frameworks you can name.”
Closing
Multi-framework compliance is the operational reality for every organization operating in Vietnam's 2026 regulatory landscape. The question is not whether you will face overlapping obligations – you already do. The question is whether your compliance architecture treats those overlaps as a design feature or ignores them until an inspection reveals the gaps.
The organizations that get this right do not have larger compliance teams. They have connected compliance operations – obligation mapping, evidence organized by framework, obligation, and owner, cross-framework visibility, and regulatory change workflows that route impact automatically instead of relying on manual detective work.
If you want to see how multi-framework compliance operations work in practice – obligation mapping, cross-framework evidence dashboards, and regulatory change management – explore AesirX ComplianceOne: https://aesirx.io/compliance-one
Ronni K. Gothard Christiansen
Technical Privacy Engineer & CEO, AesirX.io
Frequently Asked Questions About Multi-Framework Compliance in Vietnam
Laws referenced:
- Personal Data Protection Law 2025 (VN PDPL)
- Decree 356/2025 on Cross-Border Personal Data Transfer (VN PDPL Decree 356)
- Vietnam Data Law (effective 2025-07-01)
- Cybersecurity Law 2025 (effective 2026-07-01)
- Cybersecurity Decree 53
- AI Law 2026 (effective 2026-03-01)
- E-Commerce Law 2025 (effective 2026-07-01)
- Telecommunications Law 2023 (effective 2024-07-01)
- Decree 13 (PDPL implementation)
Disclaimer: This article provides general information about regulatory compliance operations. It does not constitute legal advice. Organizations should consult qualified legal counsel for framework-specific compliance guidance.